 Security
Security
New Security Update: What's Changed on Nexus
The latest platform update brings enhanced 2FA options, improved dispute resolution and new anti-phishing measures.
Read More →Nexus Onion stands as the most comprehensive informational resource about the leading darknet marketplace — covering escrow security, vendor verification, privacy-first cryptocurrency, OPSEC protocols and safe practices for the privacy-conscious user.
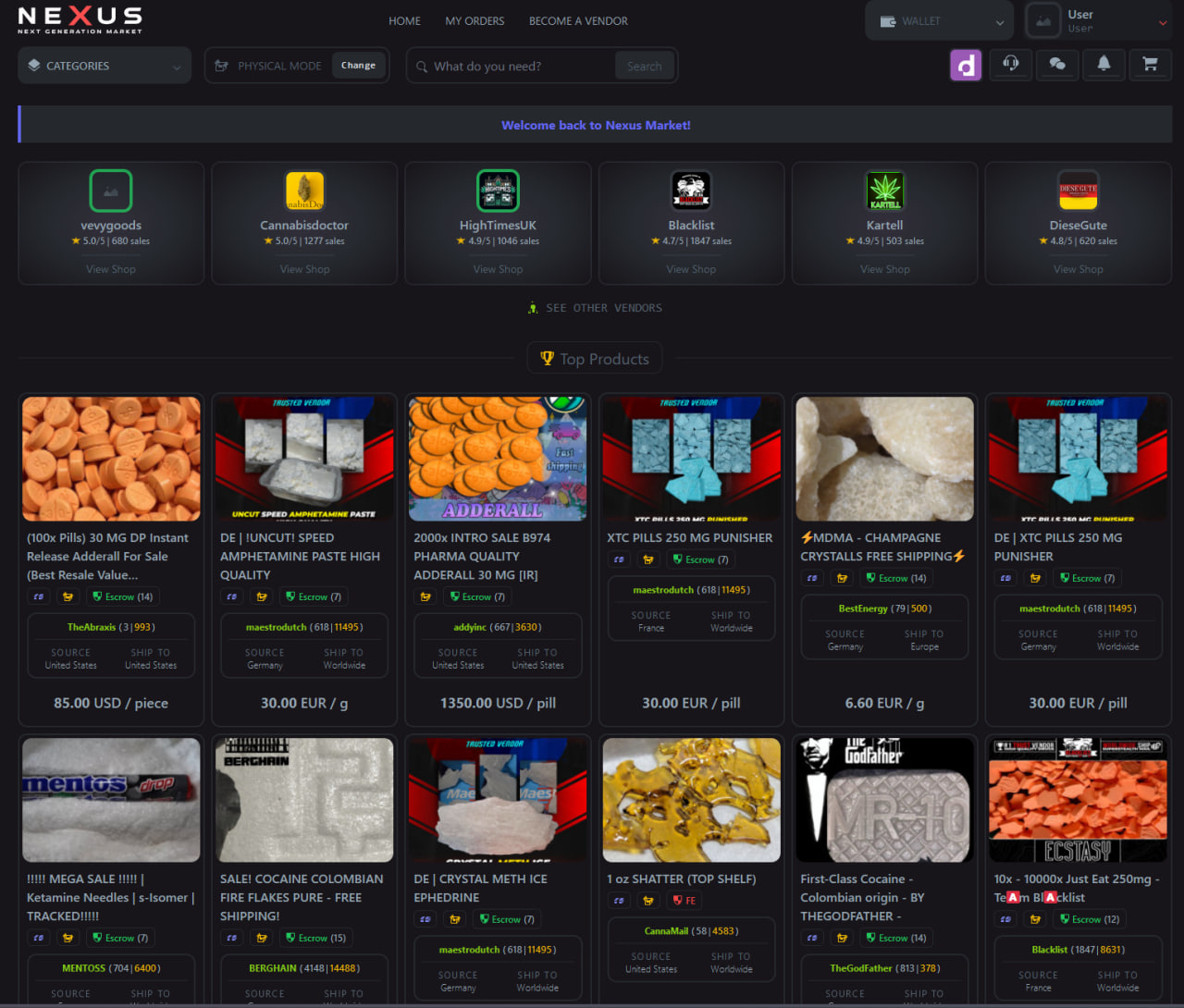
The Nexus darknet platform has set a new benchmark for marketplace security, usability and trust. Each feature below is built around one core principle: keeping users safe.
Every transaction is protected by cryptographic multi-sig escrow. Funds are only released when both parties confirm delivery — eliminating exit scams completely.
All vendors undergo a bonding and review process before listing. Community ratings, transaction history, and admin verification create a trusted seller ecosystem.
XMR is the primary payment method. Monero's ring signatures, stealth addresses and RingCT make every transaction cryptographically untraceable on the public blockchain.
All internal communications use PGP-based encryption. Messages between buyers and vendors are secured in transit and stored encrypted at rest.
The marketplace admin publishes a verified PGP key for all official communications. Users can cryptographically verify any message or announcement is authentic.
Nexus Market functions fully without JavaScript, drastically reducing your browser fingerprint and attack surface. Compatible with Tor Browser's strictest security settings.
Bitcoin emerged in 2009 as the world's first decentralised digital currency, introducing the blockchain — a public, immutable ledger of all transactions. While revolutionary, Bitcoin's transparent ledger proved problematic for privacy-conscious users: every transaction is permanently visible to anyone who inspects the chain.
This sparked the development of privacy coins — cryptocurrencies engineered from the ground up to obfuscate sender, receiver and transaction amounts. Unlike Bitcoin's pseudonymous model, privacy coins offer cryptographic anonymity by default.
Privacy coins use advanced cryptographic techniques — ring signatures, zero-knowledge proofs, stealth addresses and confidential transactions — to ensure financial privacy. The most notable are Monero (XMR), Zcash (ZEC) and Dash (DASH), each employing different approaches to achieve on-chain anonymity.
Ring signatures + stealth addresses + RingCT make every transaction untraceable. The gold standard of financial privacy. Full Monero guide →
Pseudonymous but traceable on the public blockchain. Use CoinJoin and avoid reusing addresses. Full BTC guide →
Faster block times than Bitcoin with lower fees. Similar privacy limitations — treat as pseudonymous. Full LTC guide →
 Security
Security
The latest platform update brings enhanced 2FA options, improved dispute resolution and new anti-phishing measures.
Read More → Statistics
Statistics
A detailed breakdown of transaction volumes, vendor growth, and category trends across the first quarter of 2026.
Read More →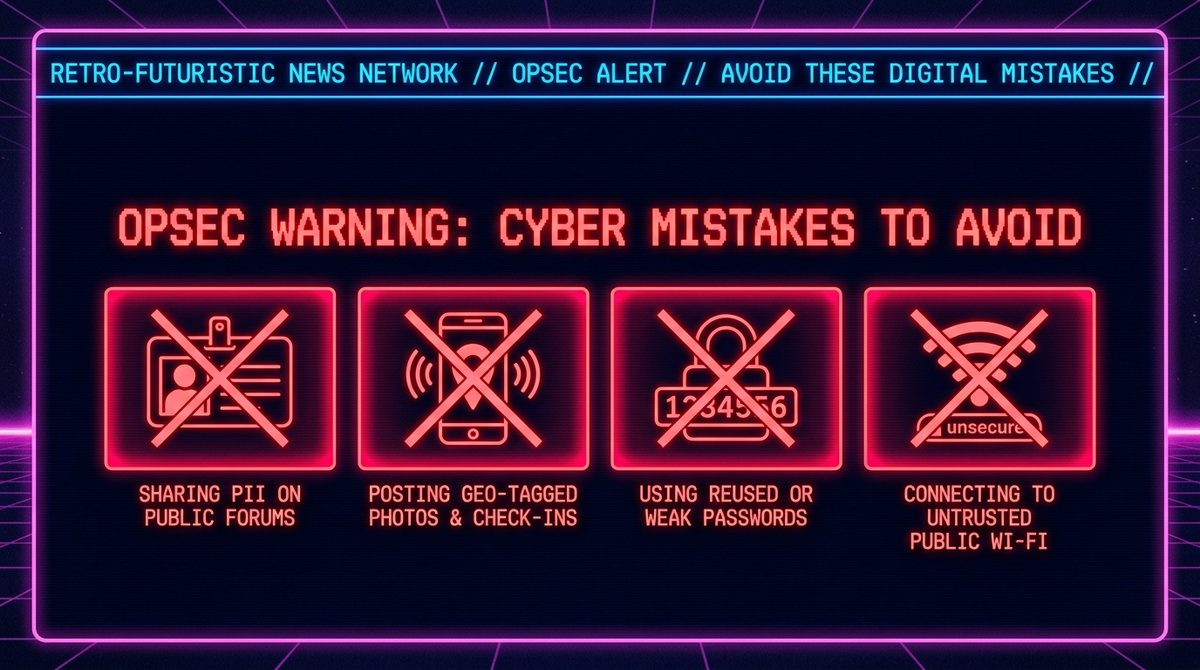 OPSEC
OPSEC
Real-world analysis of the most common operational security failures that have led to user identification.
Read More →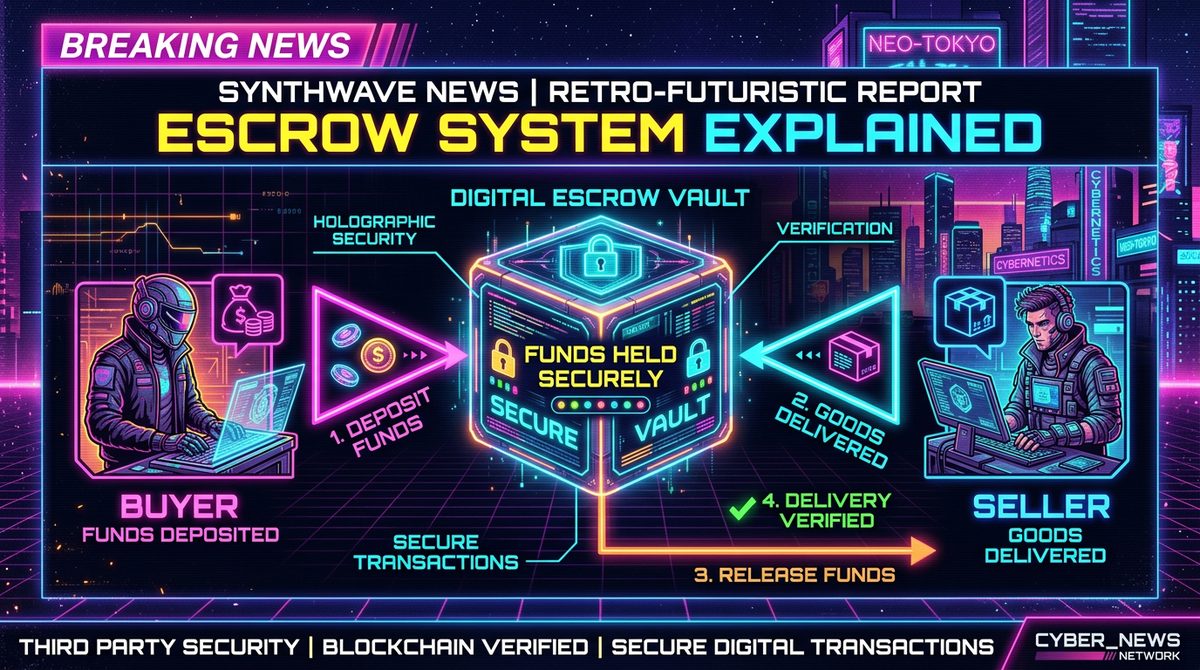 Guide
Guide
How multi-signature escrow protects buyers and why you should never skip the escrow protection offered by Nexus Market.
Read More →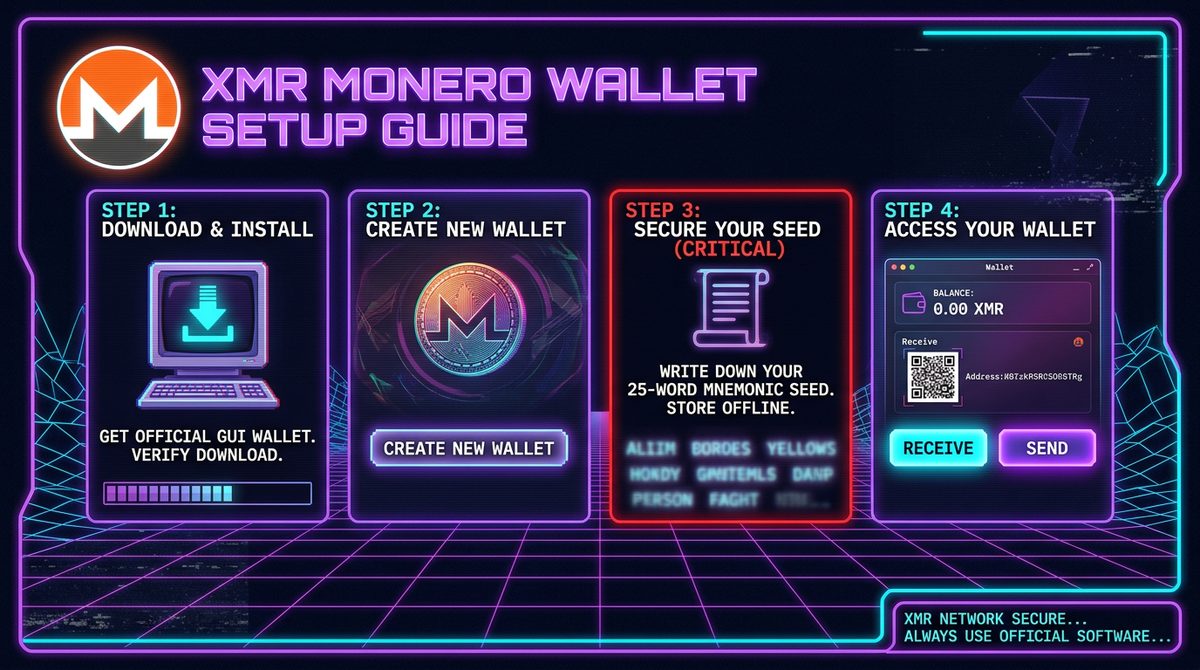 Crypto
Crypto
From downloading the official GUI wallet to making your first private transaction — a complete beginner's walkthrough.
Read More →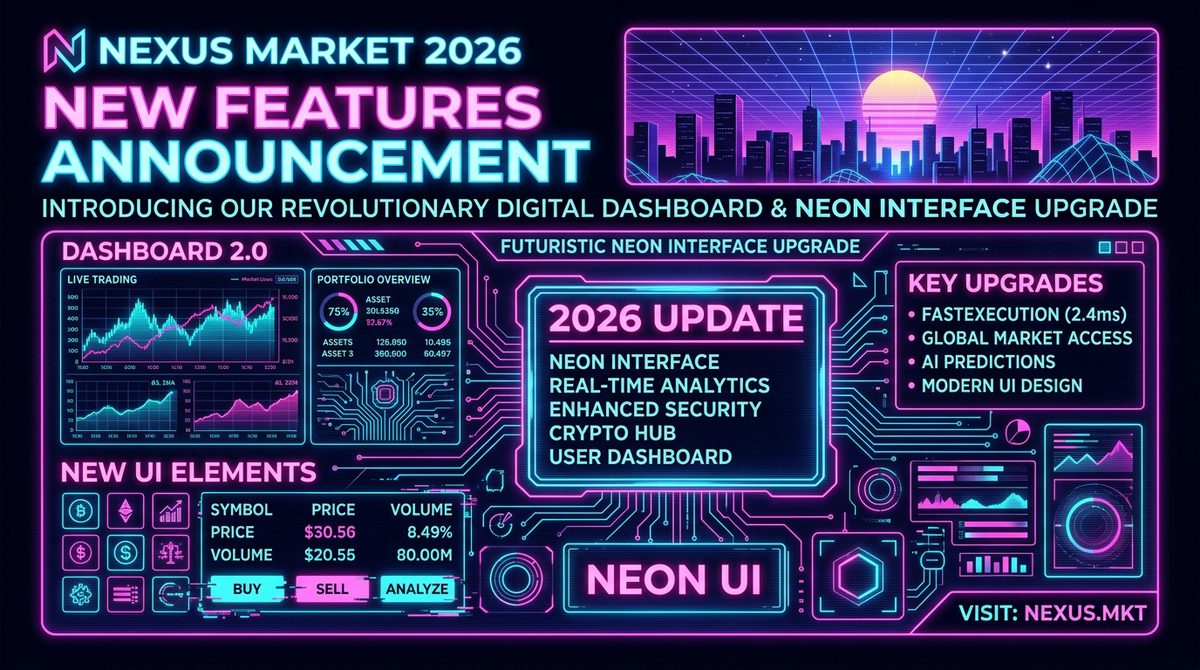 Platform
Platform
The platform rings in the new year with a revamped vendor dashboard, improved search and enhanced order tracking.
Read More →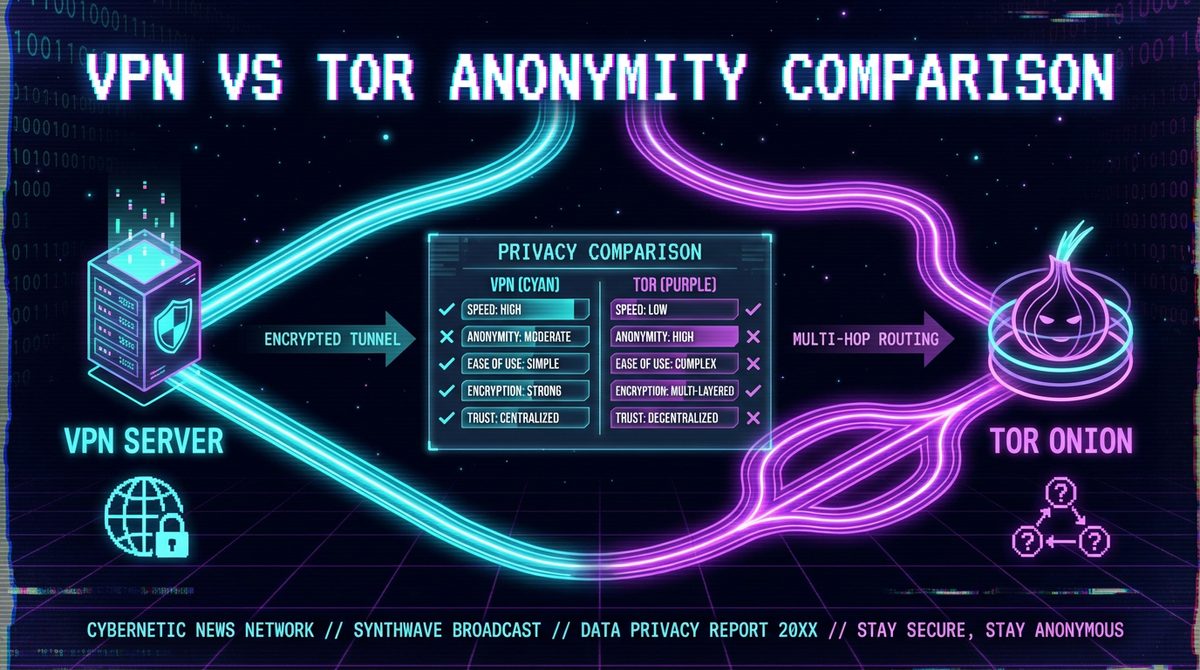 Privacy
Privacy
An honest comparison of VPN and Tor for darknet users — when to use each, how to combine them, and the risks of each approach.
Read More → Safety
Safety
Phishing clones are the #1 cause of fund loss. Learn how to identify fake sites and protect yourself before entering any credentials.
Read More →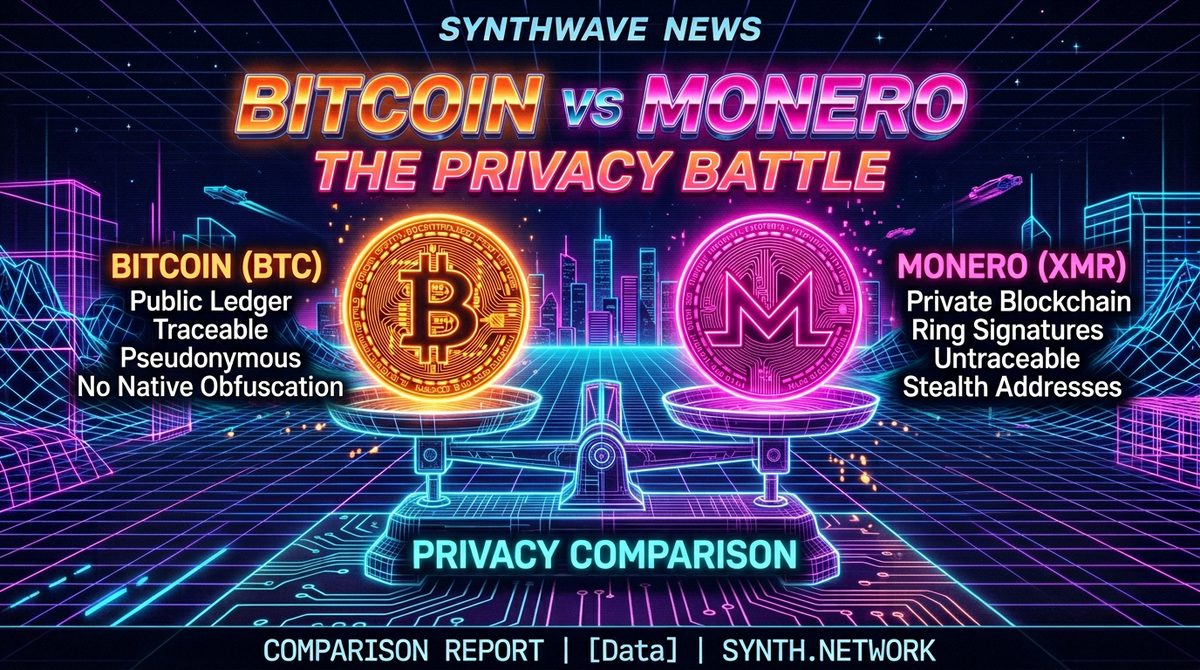 Crypto
Crypto
An in-depth technical analysis of why Monero's privacy guarantees are fundamentally superior to Bitcoin's pseudonymous model.
Read More →This section is purely informational. Harm reduction is a public health approach that aims to minimise the negative consequences associated with substance use without requiring abstinence. Knowledge saves lives.
Always begin with the lowest effective dose, especially with substances from unknown sources. Potency varies significantly between batches and suppliers.
Fentanyl test strips and reagent testing kits (Marquis, Mecke, Simon's) can identify dangerous adulterants. Never skip this step. Available from harm reduction organisations.
Always have a trusted, sober person present or accessible. Set up a check-in system if using alone. Know the signs of overdose for every substance you use.
Naloxone (Narcan) reverses opioid overdoses. Carry it. Know how to use it. It is available at pharmacies and harm reduction centres in most countries.
Certain drug combinations are lethal — particularly opioids + benzodiazepines, stimulants + MAOIs, and depressants combined with alcohol. Always research interactions on TripSit.
In an overdose emergency: call emergency services immediately. Put the person in the recovery position. Many jurisdictions have Good Samaritan laws protecting callers from prosecution.
Operational security is the practice of protecting sensitive information from adversaries. For darknet users, poor OPSEC is responsible for the overwhelming majority of identifications and arrests — not technical vulnerabilities in Tor itself.
⚠ Critical: The single biggest OPSEC mistake is correlating your darknet identity with any real-world information — usernames, email addresses, writing style, or delivery addresses linked to your identity.
Phishing is the #1 cause of fund loss in the darknet space. Sophisticated clones of Nexus Market exist that look pixel-perfect but steal your credentials and funds.
Ready to access Nexus?
Get the verified, PGP-signed .onion links from our secure entry page.
Get Verified Links →All links verified with PGP signature
This Nexus Onion information portal is for educational purposes only. We provide security guidance, market information, and privacy best practices to help users navigate the darknet safely.